Acts of terrorism, drugs and weapons smuggling, fraud, and sabotage are just a few of the types of incidents that can threaten aircraft security. The fact that insiders are granted trusted access to aircraft, equipment, and critical airport infrastructure, coupled with the fact that insiders possess intimate knowledge of business operations, enables them to easily identify and exploit vulnerabilities to carry out malicious acts or criminal activity. Their potential access to systems and records can also make detection more difficult. Kara Kennedy talks about the threat trusted insiders pose to aircraft security, challenges, and defence strategies available to mitigate the risks.
It is important to note that trusted insiders may carry out acts intentionally, unintentionally (for example unwittingly introducing malware to a computer system or network), or under duress (for example, blackmail). It’s not only airline staff but also airport employees, control room operators, and an array of contractors that may have insider access or knowledge to pose an insider threat. All forms of insider activity must be considered in risk assessments for aircraft security.
Threats posed by the trusted insider can have significant consequences, not only for the safety of aircraft and passengers, but also the airline’s financial sustainability, regulatory compliance, and the reputation of the airline involved in an incident, as well as the aviation industry as a whole.
Blended Physical Security Attacks
Airline vulnerabilities may be exploited to facilitate a direct physical security attack, or a blended attack involving an attack on an information technology (IT) system to facilitate a physical security attack. For example, an IT-based electronic access control system (EACS) may be attacked and disabled to help facilitate unauthorised physical access.
The insider threat may not always be the direct source of the attack. They may pose a threat by introducing malware to an IT system, releasing confidential information, facilitating unauthorised access, or falsifying records to enable or facilitate criminal activity.
Globally, many critical infrastructure sites have fallen victim to IT attacks. Air-gapping – an IT control measure that involves physical separation of the network controlling critical infrastructure from that controlling corporate infrastructure – becomes ineffective when it comes to the trusted insider threat. Stuxnet, a malicious computer worm, which allegedly attacked an Iranian nuclear facility in 2010, was said to be delivered via a USB flash drive, illustrating that extremely high security facilities are still at risk, irrespective of whether or not systems are air-gapped.
Targeted social engineering emails have become more sophisticated and prevalent in recent years and continue to pose a real threat to the security of IT networks. In particular, phishing attacks, which send carefully constructed emails that appear to be from a trusted source, aim to trick a trusted insider into clicking on a malicious link or downloading a malicious file. This can lead to an adversary gaining unauthorised access to a network, gaining access to sensitive information, gaining an understanding of business systems and processes, identifying vulnerabilities, or infiltrating control systems.
Insider Case Studies
Information pertaining to the following case studies was obtained through open source publications and media reporting.
“…a pilot had confronted this same employee after observing him exhibiting suspicious behaviour within a cockpit of a parked aircraft almost 12 months earlier…”
In March 2009, whilst Coca-Cola was attempting a US $2.4 billion foreign takeover of juice company China Huiyuan Juice Group, they allegedly fell victim to a state-sponsored cyber-attack. Media reports claim a phishing email was sent to Coca-Cola’s deputy president, purporting to be from an internal legal executive and containing the subject line “Save Power is Save Money (from CEO)”. The email contained a malicious link, which allowed installation of various hacking tools and granted the hackers access to the internal network and information contained within. It appears the hackers had done their research because at that time, Coca-Cola were running initiatives to reduce their energy consumption.
The US $2.4 billion acquisition was set to be the largest in history, however it eventually fell through for reasons unknown. It is easy to see how aviation employees could be the target of a similar social engineering attack.
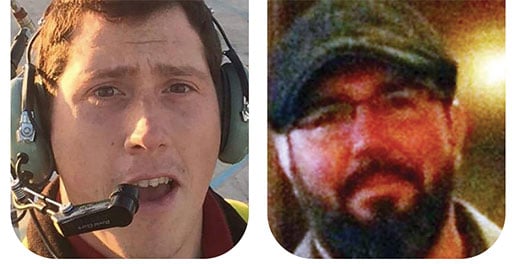
On 10 August 2018, a 29-year old Horizon Air ground service agent stole an empty Horizon Dash 8 Q400 aircraft from Seattle-Tacoma International Airport and took it on a 75-minute joyride before crashing into the sparsely populated Ketron Island, about 14 miles (23 km) south of Seattle CBD in the state of Washington. The employee was killed in the incident, however there were no other casualties involved. During his joyride, he spoke to air traffic controllers who tried to talk him down. In the transcript, he talks about himself as, “Just a broken guy, got a few screws loose, I guess. I never really knew it until now.”
The employee had worked for the airline for over three years before this incident occurred. Thankfully this suicidal man wasn’t out to hurt anyone but himself. After the incident, the media reported that a pilot had confronted this same employee after observing him exhibiting suspicious behaviour within a cockpit of a parked aircraft almost 12 months earlier.
This incident illustrates how an unlicensed ground worker with the ability and intent to steal an aircraft, could easily find the opportunity required to start an aircraft, drive to the runway and take-off unassisted, then fly the aircraft in acrobatic manoeuvres and, at times, upside down, with apparently no pilot training whatsoever and nothing in place to stop him. If he had the intent to hurt innocent people, he certainly could have done far greater damage and no doubt taken many innocent lives. It also demonstrates the importance of having an insider threat mitigation strategy, and a strong security culture so that employees understand how to both recognise and report red flags within the workplace.
“…within minutes, radar feeds, flight plans, and other data which controllers rely upon to direct more than 6000 aircraft per day across the USA had vanished…”
Motives for these types of acts are not always terrorist related. Trusted insiders suffering from mental illness pose significant risk to aircraft security, as do trusted insiders who are disgruntled with their employer, or those who are driven by other motivators such as money, revenge, ideologies, coercion, or simply ego.
On 31 October 2015, a Russian Metrojet aircraft departed Sharm-El-Sheikh International Airport in Egypt and exploded mid-air 23 minutes into the flight to Saint Petersburg, Russia. All 224 passengers and crew were killed. After the incident, the Sinai Branch of Islamic State of Iraq and the Levant (ISIL) claimed responsibility for the incident and published a photograph of the alleged bomb used to bring the plane down in an online extremist publication. There was much debate about the true cause of the crash, however after the investigation took place the Egyptian president acknowledged that terrorism was in fact the cause. There were unconfirmed reports that a mechanic whose cousin was a member of ISIL, two airport police officers, and a baggage handler were all implicated. Less than a year later, in March 2016, Metrojet filed for bankruptcy. Despite the insider reports being unconfirmed, this is an example of how an incident such as this can critically impact an airline’s reputation, and essentially lead to its financial demise.
On 26 September 2014, a communications technician with 27 years’ experience set fire to a communications room at the Chicago Air Route Traffic Control Centre. Within minutes, radar feeds, flight plans, and other data which controllers rely upon to direct more than 6000 aircraft per day across the USA had vanished. Due to the intimate system knowledge the contractor held, he was able to target key components for destruction and reportedly pulled back steel sheathing on fibre-optic data cables to maximise damage. He also destroyed back-up communication feeds. The incident resulted in thousands of flights being displaced or cancelled and the system needing to be replaced. It took several weeks to return to normal operations.
The incident was reported as the “worst case of sabotage in the history of the nation’s air-traffic control system”. Emergency responders found the suicidal employee at the site of the fire after he had attempted to take his own life. A Facebook suicide post was revealed, which included anti-US Government claims of “immoral and unethical acts”. He was later sentenced to over 12 years in gaol for the act of sabotage. Even though all affected flights were grounded safely, this incident caused a very serious risk to aircraft safety, and represents a prime example of how much damage one disgruntled contractor can cause.
The Importance of a Strong Security Culture
A workplace with a strong security culture will train staff to understand security policies, procedures, and threats to aviation. Staff will willingly comply with security requirements. Suspicious behaviour or activities not aligned with the business code of conduct or security policy will not be tolerated, and incidents will be reported immediately and investigated without delay. Management will support and enforce security policies and, if an incident does occur, it is more likely to be identified and reported in a timely manner. Trend and root cause analysis will be conducted on any minor breaches recorded to ensure vulnerabilities are identified and that there is a process of continuous improvement.
Conversely, in a workplace with a poor security culture, compliance with security related policies and procedures will be relaxed and, if security breaches do occur, they are more likely to go undetected or, worse still, detected and unreported. The risk of malicious or criminal activity in this type of environment will be higher than that in a workplace with a strong security culture.
Employees must all play a pivotal role in contributing to aircraft security, therefore employee trustworthiness, security training, and ongoing security awareness are all key elements to building a strong security culture. More often than not, security incidents or suspicious behaviour are identified by employees.
Defence Against the Trusted Insider Threat
Defence against the trusted insider threat to deliver aircraft security must be holistic in nature and delivered consistently by all security stakeholders. Law enforcement agencies, regulators, and operators must all work together to maintain up-to-date regulations, develop a strong security culture within the industry, gather intelligence, and share relevant information.
Individual operators should perform a documented risk assessment that considers all forms of trusted insider threats. A trusted insider threat mitigation strategy should include:
- a training and awareness programme;
- security culture programme;
- personnel vetting procedures with pre-employment screening and post-employment aftercare;
- information sharing initiatives;
- incident trend analysis, and
- detection measures such as data mining and analysis to identify lead indicators (or red flags) within the workplace.
Ongoing dialogue and cooperation between the security department and HR department is essential to monitor employees that may be disgruntled through workplace issues, or employees who are exhibiting red flags such as symptoms of drug or alcohol problems, behavioural issues, circumventing security measures, displaying sudden changes in personality, or suffering from an addiction such as gambling, which may be impacting their performance at work.
Aircraft security is something that cannot be achieved in isolation when it comes to the insider threat. It takes a multifaceted approach and conscious cooperation between internal and external airline stakeholders to tackle this challenging issue.

Kara Kennedy is the founder of a company that provides expertise in security risk management and strategic planning, specialising in managing the risk of trusted insider threats and security culture. Kara has over 20 years’ experience in the security industry and, in a previous role, wrote the trusted insider threat mitigation strategy for Australia’s only nuclear reactor facility. Kara has extensive experience in critical infrastructure protection and transport security. Based in Sydney, Australia, Kara can be contacted at kara@yourbusinesssecurity.com.au
