New drugs, routes and tricks spur operators and vendors toward smarter, faster, safer devices.
Air, ground, maritime and rail operators as well as enforcement officials face rapid changes in drug smugglers’ tactics, while detection vendors that support them are refining technology — including artificial intelligence (AI) — for products to help foil the crooks.
Tougher enforcement efforts around the world, greater supplies and higher prices have spurred smugglers to decentralize their organizations, outsource methods and diversify routes for moving narcotics, such as “designing” more potent drugs that can be shipped in smaller, less detectable parcels.
“The traditional smuggling routes and methods have not changed significantly,” said Jeff Sweetin, a retired U.S. Drug Enforcement Administration (DEA) special agent and counter-narcotics consultant for Thermo Fisher Scientific. However, he and his colleagues have seen “several methods of countering added border enforcement. While these trends have not yet amounted to a complete shift in cartel tactics, enforcement personnel are reporting them more frequently.”
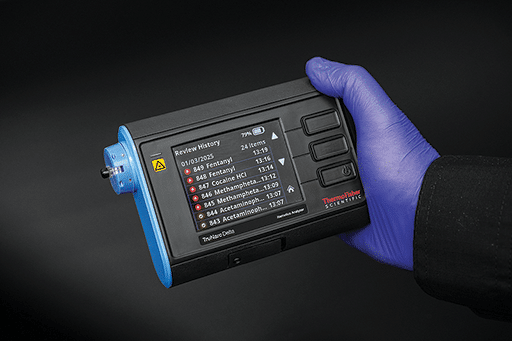
Thermo Fisher in May unveiled the TruNarc Delta and Tau upgrades of its handheld narcotics analyzer, which uses Raman spectroscopy for rapid, non-contact identification of more than 1,200 substances. The Delta is aimed at U.S. customers, the Tau for others worldwide.
Vendors look to build on their portfolios of proven spectroscopic- and radiation-based detectors by increasing the speed, range and adaptability of results for field investigators, in part with AI-based tools. For instance, they are linking detector results with cloud-computing libraries of spectroscopic signatures that can detect specific drug ingredients from tens of thousands of possibilities within seconds and can learn new signatures without the need to add them manually.
Smugglers’ New Tactics Vary
Many have foregone top-to-bottom supply chain control and outsourced shipping phases, processing stages and money-laundering. Police have seized single bulk shipments that contained drugs labelled for competing gangs and destined for a multitude of customers — an Amazon-like model for saving money and speeding delivery. Cryptocurrency is replacing cash to evade scrutiny as payments change hands.
More roundabout routes are adopted — say by ship from Latin America to West Africa on to Scandinavia and Russia, then by truck to inland points — to break patterns that make police suspicious. Some smugglers have moved upstream products like coca paste from Latin American cocaine labs to final processing closer to consumers in Europe and fentanyl powder to pill pressers in the U.S. Others are experimenting with liquifying drugs to hide them in fuel tanks, seat cushions and insulation, Sweetin said. Smugglers are hiding drugs in auto batteries and masking them with chemicals to throw off detectors.
Some are developing submersibles to sail tons of drugs between continents, even as far as Europe and Australia. There are reportedly smugglers hiring professional divers to attach drug shipments outside cargo ship hulls then fly to the destination to remove them.
“Illicit trafficking networks have evolved into increasingly industrialized criminal economies that exploit weaknesses in border security, customs controls and screening technologies,” Smiths Detection, aviation marketing manager for Smiths Detection, said. “This shift is creating distinct smuggling patterns across all major modes of transportation.”
He added, “While the methods differ across transport modes, they share a common thread: growing sophistication that poses significant new challenges for global border security.”

hold-baggage and air cargo screening system. Smiths image.
Smiths in October released the SDX 10080 SCT, the latest product in the global EDS line. It is a modular hold-baggage and air cargo screening system that combines advanced dual-energy computed tomography (CT) with an optional high-resolution dual-view line scanner that Smiths said “offers exceptional modularity, reliability and efficiency.”
Among its other products is the HCVM XL mobile scanner, which provides high-energy X-ray imaging for non-intrusive inspection of cargo to enable customs officers to rapidly and accurately identify illicit goods without disrupting the flow of trade. At the turn of the year, Smiths installed four with Trinidad & Tobago’s customs agency at Port of Spain and the Port of Point Lisas.
Efforts to counter new drugs and tactics are bolstered by greater counter-drug funding, particularly in the U.S. and Europe.

That increased funding “will institutionalize demand” in the narcotics-detection and related markets and support growth in them, said the CEO and co-founder of 908Devices, Kevin J. Knopp. “This is setting up not only in the United States, but globally.” One recent report forecasts the global market for narcotics detection equipment to grow from $3.76 billion last year to $5.05 billion by 2029, maintaining a compound annual growth rate of more than six percent.

Additional funding in the U.S. includes this year’s budget reconciliation law and last year’s DETECT Fentanyl and Xylazine Act, which should boost research and development of means to detect those drugs.
In October, 908Devices said the U.S. Coast Guard bought 23 of its MX908 handheld mass spectrometers for narcotics interdiction efforts and hazardous threat detection. The service now fields more than 35 of the MX908, which combines thermal desorption, chemical ionization and high-pressure mass spectrometry to detect hundreds of chemical substances at trace levels, including fentanyl, explosives and other threats. The MX908 can identify over 2,000 fentanyl analogs, the company said.
In Europe, funding boosts stem from increased defense funding by NATO members and others. Customers are showing greater interest in detection capabilities elsewhere in the world, too. For instance, Bruker Corp. saw a 30 percent year-over-year increase in orders for its airport-deployed detectors, related consumables and services through October.
“There are significant improvements outside of the U.S.,” Bruker president and CEO Frank Laukien said, including in Europe, Japan, China, South Korea and the Middle East. He added that the company’s Applied Markets segment is “growing very nicely” with “a pretty broad international distribution.”

Bruker’s products include the Road Runner, a 7.5-pound, handheld device to detect narcotics and explosives vapors and particles. It uses ion mobility spectrometry (IMS) with a compressed high-intensity radiated pulse (CHIRP) algorithm and guides its user step by step via a touchscreen display. Another product is the Mobile-IR II, a portable, battery-powered Fourier Transform Infrared (FT-IR) spectrometer that the company said delivers laboratory-level spectral performance with an intuitive workflow set-up for IDing illegal substances.
The greater funding also stems from Europe’s efforts to combat a spike in cocaine use there (which now may exceed that in the U.S.). “Belgium, the Netherlands and Spain have reported the highest volumes of seizures, reflecting their importance as entry points for cocaine trafficked to Europe,” said a March report by the U.S. State Department’s Bureau for International Narcotics and Law Enforcement. That has increased cross-border criminal activity, “with European organized crime groups expanding their footprint in Mexico and South America and vice versa.”
Facing such crime, geopolitical conflicts and terrorism, “governments worldwide are investing heavily in advanced systems to enhance detection, deterrence, and response capabilities,” said Ajay Mehra, president, CEO and director of OSI Systems. He added customers are addressing the growing threats by increasing their focus on technology innovation and shifting policy priorities, supported by targeted funding.
OSI Systems designs and manufactures specialized electronic systems and components for critical applications, serving customers in 170 countries. Its Rapiscan Systems unit offers a wide range of scanners and inspection systems for aviation security, cargo, and vehicles.
These include the MobileTrace simultaneous dual-mode narcotics/explosives detector, which uses the company’s patented Ion Trap Mobility Spectrometry. It has been deployed at airports, border crossings, military bases and other critical global checkpoints.
In September, Rapiscan launched its Orion Road 930DX-V mobile X-ray system. With a van-size footprint, the system is designed to detect narcotics, concealed weapons, explosives and other contraband for customs and border protection, critical infrastructure fortification, law enforcement and other missions.
The Threat of Drugs is Broad and Changing
Fentanyl — the synthetic drug and most potent narcotic used by doctors (50-100 times more potent than morphine) — is highly addictive. Fentanyl analogs are synthetic opioids generally engineered to be more potent; carfentanil is 100 times more so. More potent ones can be small enough for hundreds of lethal doses in envelopes to be mailed — still a major smuggling method — or hidden on the body.

“Detecting narcotics concealed on the body under clothing is incredibly challenging,” said Heather Colby, who manages sales channels and alliances for Apstec Systems. “Technology has struggled to deliver effective solutions, and large-scale manual operations are intrusive, costly and generally impractical.”

real-time screening for large numbers of passengers and their belongings. The solution identifies drugs concealed on the body while respecting privacy and ensuring a smooth border crossing experience. Apstec image.
Apstec develops high-throughput screening technology to detect narcotics, explosives and weapons. It said its products can screen large numbers of people and identify diverse threats while ensuring seamless, non-intrusive processing. It described its flagship product, HSS Falcon, as a powerful, AI-driven solution that provides comprehensive detection on people and in body-worn/hand-carried bags.

The first fentanyl analogs emerged in 2019. Last year, there were 688 reported variants, according to the United Nations. Today there are nearly 1,400.

“Drugs like fentanyl remain a deadly threat and drain on our country, consuming lives and resources across America,” said Dr. JihFen Lei, president of Teledyne FLIR Defense. In October, that company got an order from U.S. Customs and Border Protection (CBP) for 15 of its Griffin G510x portable chemical detectors, which are specifically designed to analyze and identify explosives and narcotics (such as fentanyl and its analogs) within five minutes. The instruments are to be fielded across the U.S. to help CBP identify the most challenging drug samples, such as those containing fentanyl in extremely low concentrations mixed with other compounds.
Those analogs are among a diverse group of lab-made compounds called novel psychoactive substances (NPSs). Most are created to mimic prescription or illicit drugs’ effects and to evade controlled-substances laws by slightly modifying an existing drug. With unfamiliar chemical signatures, these drugs can evade detectors until those signatures are added to devices’ libraries. Thermo Fisher’s Sweetin recalled that when traffickers began mixing fentanyl with xylazine, a pet sedative, detectors didn’t recognize it because its signature wasn’t in their libraries. Once it was added, investigators looked back and found it had been used widely.
“No matter how good the devices are,” he said, “if we don’t know to add an emerging drug to a device library, our customers can’t identify them.”

That need is one reason vendors are adding AI. In February Leidos said it was partnering the AI software company SeeTrue to improve the efficiency of airport security and customs screenings through AI-enabled algorithms for detecting prohibited items. Smiths has partnered with BigBear.ai, Deepnoid and other AI experts to hone its systems threat-detection capabilities.
The threat-detection company Autoclear offers proprietary AI Threat Assist software with its X-ray security screening systems. Its N2300 Fentanyl Trace Detector can be added to any Autoclear X-ray baggage scanner.
TactiScan’s pocket-sized narcotics scanners use cloud AI that taps advanced deep learning algorithms together with commonly used reference standards to analyze readings, identify substances and update its signature library. This reduces the risk that TactiScan will be confused by cutting agents and adulteration.
“AI and advanced analytics are transforming the detection landscape,” Smiths’ Kaufmann said. “These tools will be critical in busy logistics hubs, where authorities must assess large volumes with limited resources.
Old drugs still prevail. Around the world, the stimulants methamphetamine and amphetamine dominate the use of and trafficking in synthetic drugs, according to the U.N., and cocaine production and use is setting records year after year. The U.N. estimated worldwide illegal cocaine production in 2023 at 3,708 tons, 34.5 percent more than 2022 and 327 percent more than 2014. (Heroin production is dropping.)
Smugglers have long used aircraft, trucks and ships. They also are expanding their use of trains, which have been used mostly to traffic people. In one example, officials in India’s Kerala state said trains are now a prime narcotics smuggling method. In 2024, they said 1,232 pounds were seized on trains in the state. By this March, police had seized 928 pounds. Those totals were for only one of India’s 68 rail divisions.
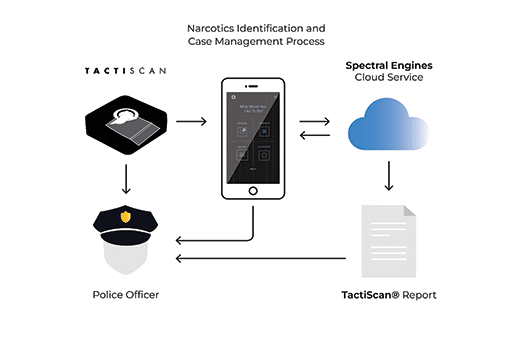
contamination and ensures the occupational safety of officers when identifying drugs.
The entire identification process is digitally documented.
That development is just one indication that drug smugglers are always seeking new markets and new ways of getting their products to them.
“Looking ahead, traffickers will remain exceptionally agile, exploiting distinct vulnerabilities across various sectors of international trade and travel,” Smiths’ Kaufmann said. “Global drug trafficking today is not constrained by geography, mode of transport, or concealment method. Countering this evolution will require next-generation detection capabilities.”