Three noteworthy numbers:
• According to Statista.com, total global trade was worth $22.3 trillion in 2021.
• According to the United Nations Conference on Trade and Development (UNCTAD), ships carried over 80% of the goods traded globally.
• 80% of $22.3 trillion is $17.84 trillion, so ships carried around $18 trillion in goods in 2021.
With trillions of dollars on the line, you would think that the world’s ships would be well-protected from cyber attacks. But you would be wrong. Thanks to antiquated IT systems, a general lack of proactive cyber defenses, and an absence of cybersecurity personnel onboard, most ships are easy targets for hackers extorting money through ransomware attacks, and hostile players wanting to wound specific nation’s economies by outright sabotage.
“Threat actors can easily disable or tamper with onboard and offboard systems,” said David Warshavski, vice president of Enterprise Security at the cyber technology and services company Sygnia. “While this may not seem critical to overall operations, it can effectively halt a ship from moving or delivering its cargo.”
Thankfully, there are steps that can be taken to bring maritime cybersecurity up to 21st century standards, and some maritime associations and shipping companies are already taking them. But others aren’t: “There are a lot of cyber deniers that are just saying, ‘Ah, this isn’t that big of a problem’,” said Gary Kessler, principal consultant in the Maritime Solutions Group at Fathom5, an industrial technology company delivering security-first solutions to the maritime industry. “Their frequent response is, ‘Has anybody sunk a ship yet with a cyberattack?’.”
Why Ships Are So Vulnerable to Cyber Attacks
When it comes to cyber attacks, “the maritime sector has unique vulnerabilities that are a consequence of its nature,” said Scott Blough, principal cyber security consultant at Mandiant, a global cybersecurity firm and Google subsidiary. For instance, “it is a worldwide industry, with 80% of all world trade touching a ship at some point in its journey,” said Ian Bramson, global head of Industrial Cybersecurity with ABS Group, which supports the safety and reliability of high-performance assets and operations. “With hackers increasingly looking to disrupt the supply chain to cause chaos and incur larger payouts, maritime operations are becoming increasingly compelling targets.”
“Furthermore, ships are rarely as segmented as traditional industrial environments,” Bramson added. “This means that attackers that gain access to one system can often move to other areas — like engine rooms or control systems — with relative ease. This lack of segmentation essentially means there are generally very few safeguards in place to stop a threat that has already breached perimeter security.”

Sygnia
Two ways to add such safeguards is through constant vigilance by IT experts onboard ships, and regular software updates to patch security holes in their IT environments. But most vessels do not have IT people onboard (or even on shore), while many have outdated computers running their ship systems.
“It’s amazing how many shipboard systems are based upon older Windows kernels such as Windows 7 and Windows XP,” said Kessler. “You can’t totally secure these systems because we’re talking about operating system kernels that are no longer supported by Microsoft.”
As for patching those shipboard computers whose operating systems are still supported by their manufacturers? Unfortunately, the VSAT (Very Small Aperture Terminal) satellite communication systems used by ships have limited bandwidth and high connection costs. These constraints make the transfer of large data files from shore to ships time-consuming and expensive, and thus impractical at sea. In other words, “pushing updates is not something that we want to be doing using VSATs,” said Kessler.
Meanwhile, when ships do get to port, installing cybersecurity updates can get pushed out of the way by other priorities. This results in those ships leaving port with their computers still vulnerable.
Then there’s the “huge population” of people who gain access to ships, Bramson told TSI. “Of particular note is the proliferation of third-party maintenance of ship systems as vendors come aboard to test and update systems at ports across the world,” he noted. “Even if these people have good intentions, each person brings a risk. It only takes one vendor accidentally using a malware-infected device to compromise the ship as a whole.”
These problems aren’t the only ones hampering maritime cybersecurity. A case in point: Government initiatives such as the U. S. Cybersecurity & Infrastructure Security Agency’s Cybersecurity Performance Goals (which are voluntary) are trying to convince shipping companies to become fully responsible for their own cyber protection. Yet those who try to do so can see their efforts stymied by vendors who restrict the application of cybersecurity controls on their proprietary products.

To make matters even muddier, there are a plethora of regulatory bodies stepping all over each other in their well-intentioned attempts to make global shipping more cybersecure. In the U. S. alone, there are over a dozen agencies that play a role in maritime security, which causes effort overlaps and waste. This confusion is made worse by a lack of international cooperation on common standards for items such as incident reporting timelines.
What Can Be Done Now
Obstacles aside, there are many ways that maritime cybersecurity can be upgraded today. Here are some of the excellent ideas offered by the experts we spoke with.
Do a Cybersecurity Asset Inventory
Improving a shipping fleet’s level of cybersecurity is not a ‘dive in and fix it’ situation. To do it right, “organizations need to start with the basics,” said Bramson. This means doing a survey of the entire company’s Operational Technology (OT) infrastructure, “and that begins with a cybersecurity asset inventory,” he said. “Only with that information can crews move onto vulnerability management. You can only protect vital systems if you know what you have and where the risk lies.”
“It’s critical to map the systems and applications (and their dependencies) that are key to the ship’s operation, and map the relevant attack vectors that would allow threat actors to disable these systems,” Warshavski observed. “Only then will it be possible to accurately prioritize deployment of security measures and logging mechanisms that facilitate early detection, and allow organizations to mitigate attacks before they fully manifest and become highly disruptive.”

ABS Group
While the cybersecurity asset inventory is underway, shipping companies need to implement continuous monitoring of their IT and OT assets now before any changes/upgrades have been made. “Having a monitoring program running 24/7/365 enables organizations to proactively better prevent disruptions to their operations by detecting anomalies in real time,” Bramson explained. “By identifying exploits and rogue devices now, organizations can gain a more complete picture of the vulnerabilities present in their system.”
Implement Basic Cybersecurity Hygiene
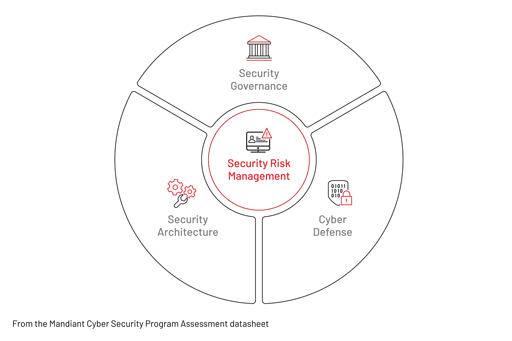
Once the cybersecurity asset inventory has been completed, it is time to detect vulnerabilities and determine what needs to be changed in a shipping company’s IT and OT infrastructure, cyber defenses, and security processes. In other words, it is time to research, develop and implement a cybersecurity plan.
Caution: companies lacking the expertise to do this in-house should seek qualified outside help, because “identifying and implementing the appropriate technologies and processes is a key element in mitigating cyber risk,” said Blough.
So, what should a cybersecurity plan tailored to a specific shipping company include? “Well, a lot of cyber defenses are built upon what we sometimes call ‘Basic Cyber Hygiene’, or ‘Cybersecurity 101’,” Kessler replied.

For instance, shipping companies and their fleets should be running, at the very least, on the latest version of Windows — with their systems having security updates installed as soon as they become available. Critical systems should be isolated and protected using complicated passwords, rather than ‘12345’ or ‘PASSWORD’. If possible, shipping companies should investigate applying the ‘Zero Trust’ security approach to their systems. Zero Trust requires users to regularly authenticate their identities as they try to access resources on the network — much like swiping an electric pass at various locked doors — rather than just signing in at a main login portal and going wherever they like unchallenged. Hackers rely on this last weakness to let them break onto a network at one point, and then wreak havoc everywhere.

Other elements of basic cyber hygiene include separating crew access to the internet from corporate access — because people download all kinds of malware unthinkingly on their own time — and not allowing USBs to be used on corporate computers unless their provenance is absolutely known. After all, hackers are known to leave unmarked malware-loaded USB memory keys in the offices they’re targeting. All it takes is for one curious employee to plug the USB key into their computer to find out what it contains, and poof! The malware is launched into their network.
The next step is to replace outdated computers and networks with systems capable of running modern cyber defensive software. “There is an adage in information security that if you take a network that is not secure and try to layer security on top of it, the result will never be as good as using a network that was designed with security in mind in the first place,” said Kessler. He added that such ‘fixes’ can end up costing “a ton of money” without providing the desired results. “It’s actually more cost-effective to rebuild your network to be secure by design.”
Take a Wide-Ranging Approach to Cybersecurity
An effective cybersecurity plan touches on all aspects of a shipping company’s business, not just its ships. This is why all elements of that business must be considered and, if need be, changed, when a cybersecurity plan is being developed.
“Policies and procedures need to be updated to include cybersecurity resilience,” Bramson said. “Policies such as Management of Change (MoC) and an Incident Response Plan (IRP) need to include changes and response procedures for critical OT equipment.”
Sometimes hackers penetrate a target company’s network not by attacking it directly, but by penetrating the network of a company supplier with weaker security, and then using that bridgehead to enter their target. This is why shipping cybersecurity teams should find ways to identify attacks on their supply chains as well as themselves. In both instances, “protecting against these attacks is a matter of monitoring operations closely, having good identity and access management protocols, and adhering to cybersecurity best practices,” said Bramson.
“Attacks through the supply chain — for example, when malicious programs are inserted into a system or device that another company uses — are of concern,” he noted. “Preventing these attacks relies on rigorous acceptance and cyber testing of new equipment to identify anomalous behavior that could indicate deficiencies in the system.”
A wide-ranging approach to cybersecurity is not a one-shot deal. Once in place, it shapes everything the company does from now into the future. For example, “one of the most important things that companies should be doing is incorporating cybersecurity throughout all stages of the system development life cycle,” said Blough. “Including cybersecurity in activities such as business requirement reviews ensures that security issues are considered in these requirements and budgets before acquisition. Companies should also incorporate threat modeling into their IT system development lifecycle to proactively identify risks. Early adoption of cybersecurity requirements increases the efficiency and lowers the cost of cybersecurity controls compared to adding after development has been completed.”
Prepare for Penetrations
Reality check: The best cybersecurity defenses will be penetrated at some point, due to the inevitable synergy between hacker cunning and company bad luck. This is why the best cybersecurity plans assume that this will happen, and have proactive measures built in to limit and control the damage.
Preparing for penetration lies in staying aware of the latest cyber threats, so that shipping companies can identify and respond to them as soon as they breach the cyber defenses. “Be familiar with the ‘Battle Terrain’,” Warshavski advised. “Attacks will happen inside defended corporate networks, and our experience shows that companies that had a good understanding of their technology and security stack, across networks and cloud platforms, were better positioned to utilize the tools they already have to fend off attacks as they happened.”
Repelling penetrative attacks successfully also requires lots of pre —attack preparations, which is part of an effective cybersecurity plan. Fortunately, there are lots of after-attack response models to choose from. “One such framework that the U. S. government promotes is the NIST Cybersecurity Framework (CSF) and Risk-Management Framework (RMF) that is designed to help organizations manage their cybersecurity risk,” said Blough. “This approach allows organizations to efficiently focus resources on the appropriate areas based on risks specific to that organization rather than the alternative inefficient ad-hoc approach.”
A third element of effective after-attack response is putting together the company’s Response Team long before anything actually goes wrong. “Once an attack is discovered, there are multiple parties that have to be aligned to facilitate a swift response and recovery effort — Legal, PR, insurance, negotiators, Forensics, external IT support; just to name a few,” Warshavski said. “More often than not, some of these are various parties that have to work in perfect sync. It’s imperative to get them all in one room before an incident occurs, to ensure that procedures and proper lines of communications are properly established beforehand.”
Once all of this is in place, it is vital for shipping companies to stage cyber attack simulations on a regular basis, so that their people and procedures stay sharp and ready to respond appropriately. “Employees need to know what their role will be should an attack happen, so they can jump into action when the time comes,” Bramson said. “Cybersecurity incident response plans not only need to be established and maintained, but also to be practiced. As with other types of drills, such practice helps people cope with ‘if it happens’ situations, while improving their response times and decision-making during an actual event.”
One Last Thought
Given just how vulnerable many ships are to cyber attacks, and how central IT functions are to keeping modern vessels running safely and smoothly, the time has come for shipping companies to put this expertise onboard as a matter of course.
“I think having a bridge officer on board every vessel with informed responsibility for IT operations and cybersecurity is a place that we need to go,” said Kessler. “You need someone onboard who can look at an incident affecting the ship’s IT systems who can tell if it is user error, a bug or a cyber attack. Right now, many bridge crews can’t tell the difference between an act of God and an act of an intelligent actor when something goes wrong with their computers — and this just has to change.”